In January, you probably heard about the SolarWinds Orion hack, the Russian-linked cyberattack that may have affected up to 18,000 government agencies and private organizations. But, chances are, you may not have heard about a key detail related to how hackers carried out this particular attack—and why this matters to colleges and universities.
The SolarWinds hack revealed a gaping hole in how many organizations—colleges and universities included—approach vendor risk management, with lessons for anyone accountable for student data security. How can institutions build a complete assessment of vendor risk into their ongoing vendor management processes?
Understanding the Challenges
While many aspects of this attack mimicked past attacks, this one took a novel approach. Instead of injecting malicious code into specific servers or using another common hacking technique, the SolarWinds hackers infected a software update. This approach meant that the corrupted code would disguise itself as an allowed file and pass into the client's solution undetected. Because many companies and organizations avoid ongoing vendor risk management, there was little attention paid among SolarWinds' clients to whether the company's software update process was secure.
Similarly, at many institutions, vendor management is more about ensuring that the acquisition of a technology solution adheres to institutional standards at the contract phase than it is about informing the ongoing management of the relationship between a vendor and the institution. This approach is insufficient as vendors continue to enhance and update their products post-contract signing, usually following some software development process. This ongoing enhancement and updating can lead to risks, such as insufficient security testing, that could later affect the institution.
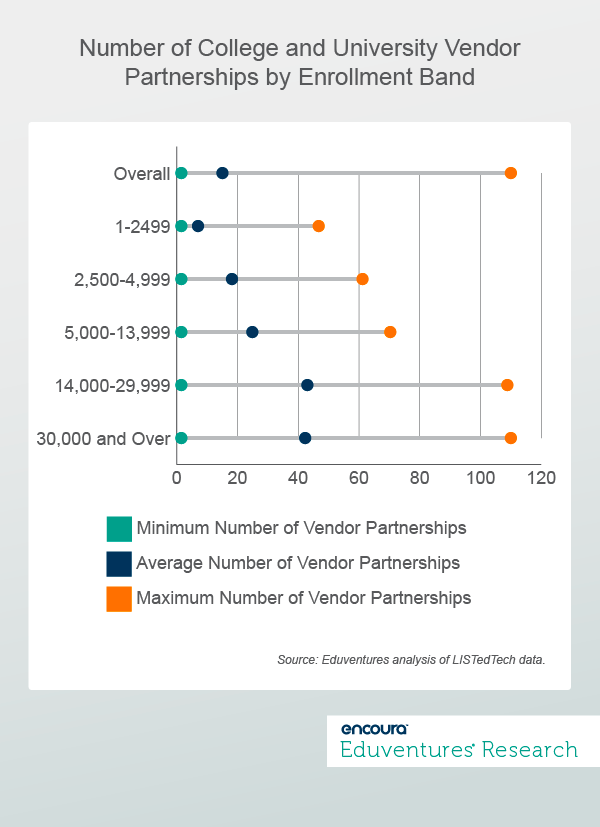
Likewise, Figure 1 shows that according to data from LISTedTech, institutions—regardless of enrollment size—manage many vendor partnerships, with an overall average of 15. This high number of vendor partnerships makes it challenging for leaders to maintain a general up-to-date sense of their vendors' risks.
Overcoming the Challenges
Organizations, such as Educause's Higher Education Information Security Council (HEISC), have done an excellent job addressing vendor risk and vendor management issues by developing tools like the Higher Education Community Vendor Assessment Tool (HECVAT). Our take, however, is that these tools concentrate on the typical pre-contract phase and overlook the control of the entire vendor relationship.
Our approach stresses the need to have greater insight and oversight into the ongoing vendor software development process. In addition to the advice of Educause, we recommend institutions take the following steps:
- Know your universe. The high number of vendor partnerships institutions manage presents challenges for leaders to understand and track each partnership's risks. Therefore, these leaders must begin this processing by wrapping their heads around the answers to essential questions: How many vendors do we partner with? How many of these vendors touch sensitive data or systems? Have we performed any pre-contract risk reviews?
- Review software update processes. As the SolarWinds hack shows, it is critical to understand how vendors manage, secure, and deliver software updates and provide the option to undo or "rollback" an update if installing it results in issues. To provide this understanding, institutions, such as the University of California, have included the ongoing review and approval of updates in their vendor risk assessment approaches. You can do this by requiring vendors to present any security testing results during the software update process.
- Recognize that managing risk is enterprise-wide. Managing technological risk is not only about preventing security breaches. It also includes providing effective, institution-wide management of systems and processes and ensuring compliance with any applicable regulations (such as handling health-related data per the Health Insurance Portability and Accountability Act). Institutions, like Case Western University, have created a governance, risk, and compliance (GRC) structure by assembling individuals from across the institution that identify and manage risks.
The Bottom Line
Most vendors may not require such a deep level of oversight; many follow technological best practices and ensure that their solutions will not increase the risk of problematic issues. That said, even the best-laid vendor plans and activities may fail. Even the most competent, well-intentioned vendors still cannot always anticipate the vulnerabilities of their software products as we have seen in recent student data breaches at Stanford University and Michigan State University.
Accepting our approach demands that schools remain vigilant over their vendor partnerships from beginning to end and require . Likewise, it requires that these leaders understand their risks with vendors and transactions and gain a deep understanding of how risk plays out across the entire school.
To be clear, we are not trying to incite panic. Instead, we want to show that institutional leaders should approach the ongoing partnership with vendors with a healthy dose of skepticism and take continuous steps to confirm that each vendor they work with adheres to the best ways to implement, manage, and update software.
Never Miss Your Wake-Up Call
Learn more about our team of expert research analysts here.
Eduventures Principal Analyst at ACT | NRCCUA
Contact
We’re accustomed to a personalized experience in all aspects of our lives – from how we shop to how we stream TV and navigate digital media. And students today are expecting the same in Education. They want a personalized experience that helps them navigate their unique paths. The COVID-19 crisis has accelerated Education’s transition to a digital experience driving us to an inflection point where delivering a truly personalized experience is right around the corner. Eduventures Principal Analyst James Wiley and Blackboard CEO Bill Ballhaus discuss how a personalized experience, fueled by data, is unfolding in education and what that means for the future.